Cyber-attacks and threats are one of the main risks facing companies and organizations today, and that is why the need for people specializing in computer forensics is growing.
Any traces of the cyber-attack and any traces left at the scene must be gathered and investigated very carefully. It is only from this point on that the forensics examiners and investigators can answer the questions of "who, what, where, when, and why."
It is important to bear in mind that the field of forensics is very broad in nature. Specialists not only help in the case of cyberattacks, but they can help in numerous other criminal investigations like child pornography and even murder.
What is Computer Forensics?
Computer forensics is a branch of forensic science that deals with the application of computer-based investigative processing methods to collect and preserve evidence in a manner that is legally admissible.
That means that a significant aspect of computer forensics science resides in the capacity of the forensics specialist to deliver results in a manner that is appropriate and accessible in a legal context.
The purpose of computer forensics is to conduct a systematic investigation on a computer device to figure out either what happened or who was responsible for what happened while preserving a properly recorded chain of evidence in a comprehensive report.
Although computer forensics may have historically been used in the fight against crime by law enforcement agencies such as the police, the use of computer forensics has expanded.
It is no longer just used by law enforcement, as personal and business entities have embraced its application for a wide variety of purposes. In fact, large corporations can even employ a team of experts on staff - especially in banking.
Applications of Computer Forensics
There are various applications of computer forensics. They span from aiding law enforcement officers in child pornography investigations to investigating fraud, murder, terrorism, rape, and cyber-stalking.
Commercial companies have used computer forensics in the private sector to prosecute a wide variety of cases involving industrial espionage, fraud, intellectual property theft, and falsifications.
Computer forensics is an important and essential instrument for combating cybercrime. In addition, it is also used to examine employee disputes, regulatory enforcement, bankruptcies, and improper usage of a workplace device, internet, and email.
The practice of computer forensics is really responsible for providing facts, reports, and conclusions that are legally permissible. To maintain the credibility of their work, computer forensic investigators must obey certain rules and guidelines.
Computer Forensics Standard Procedures
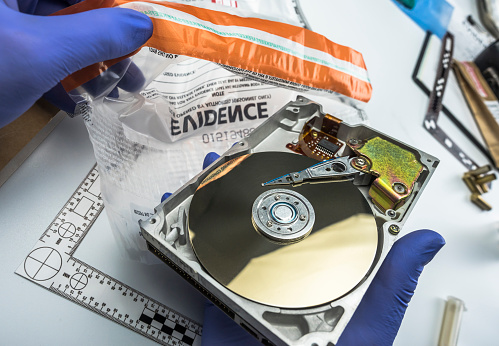
First, the investigators make a digital copy of the storage media of the device after physically isolating the device in question to ensure it can not be compromised.
Once copied, the original media is locked in a secure facility to preserve its pristine state. All work is conducted on the digital copy.
Then, investigators use a range of forensic methods and specialized tools to inspect the copy, search for secret directories, and unallocated disk space for copies of lost, encrypted, or compromised files.
Lastly, any information contained in the digital copy will be recorded appropriately in a "finding report" and checked in preparation for court proceedings, including discovery, depositions, or real litigation with the original.
Conclusion
As in many other fields, some problems restrict or adversely affect the computer forensics expert's output. The number one challenge facing a forensic analyst is the method of encryption.
Computer forensics, with subsequent coursework and qualifications, has become its own area of scientific expertise. The area is extensive, and the amount of knowledge and work required often changes on a case-by-case basis.